Axios Supply Chain Attack Exposes Crypto Apps to Risk
On March 31, 2026, a supply chain exploit hit the Axios npm library via a hijacked maintainer account, injecting a cross-platform RAT.
Quick Take
Summary is AI generated, newsroom reviewed.
Malicious versions [email protected] and 0.30.4 install a remote access trojan (RAT) via a hidden dependency, [email protected].
The attack bypassed GitHub OIDC verification, indicating a manual publish from a compromised "classic" npm access token.
Impacted systems across Windows, macOS, and Linux risk the theft of private keys, API tokens, and sensitive crypto-wallet data.
Developers must check lockfiles for these versions and immediately roll back to 1.14.0 or 0.30.3 to secure their environments.
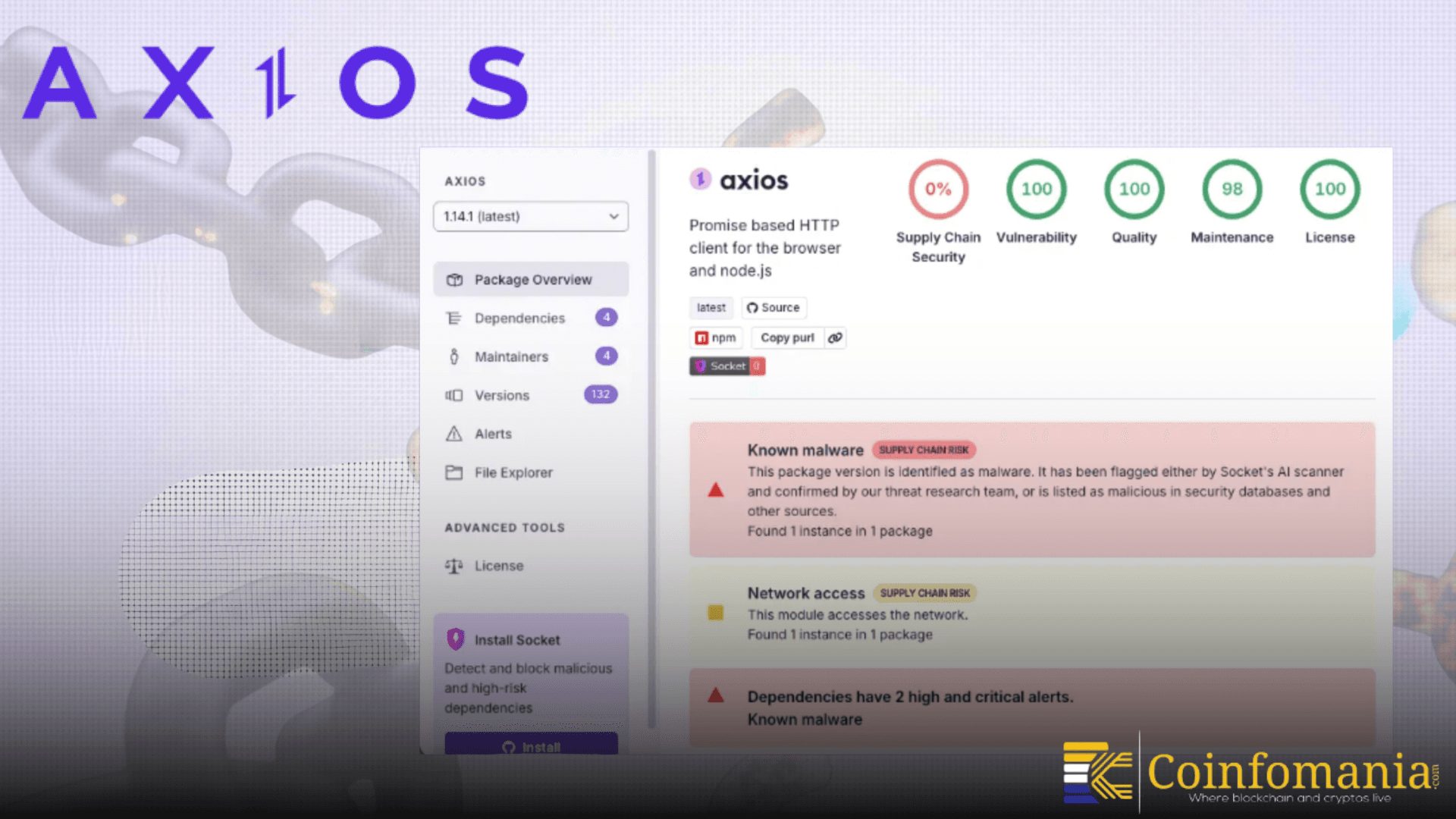
A serious supply chain attack has hit Axios, one of the most widely used tools in web development. Security researchers from Socket Security found that hackers injected malware into specific versions of the library published on npm.
🚨ALERT: According to @SocketSecurity, a supply chain attack on Axios, a widely used JavaScript library that lets apps and websites communicate with servers, resulted in hidden malware being injected into its npm distribution by an unknown attacker.
— SolanaFloor (@SolanaFloor) March 31, 2026
The attack could impact… pic.twitter.com/ooPhbHGSO7
This attack could impact millions of crypto apps. It includes many crypto platforms that rely on Axios to connect with servers. Because Axios is used across so many systems, the risk is wide and immediate. The affected versions include [email protected] and [email protected]. Developers who installed these versions may have unknowingly exposed their systems.
How the Attack Happened?
The attack did not come from a simple bug. Instead, hackers used a supply chain method. This means they targeted the software distribution process itself. In this case, attackers added a malicious package called “[email protected]” as a hidden dependency. This package was not part of Axios before. Someone inserted it quietly during the release.
Even more concerning, the release did not follow Axios’s normal process. It did not appear in official GitHub tags. This suggests the attacker gained unauthorized access to the publishing system. Reports indicate that a maintainer account may have been compromised. This allowed the attacker to push the infected version directly to npm.
What the Malware Can Do?
The malware is not harmless. It installs a remote access tool, also known as a RAT. Once inside a system, it can run commands, collect data and connect to external servers. It works across macOS, Windows and Linux. The attack is also designed to hide itself. It runs during installation and then removes traces of its activity. This makes it harder to detect. With this, even developers may not realize their system has been affected.
Why Crypto Projects Are at Risk?
Crypto apps often rely on tools like Axios to send and receive data. This includes wallet services, exchanges and decentralized apps. If these apps use the affected versions, attackers could access sensitive data. This may include private keys, API tokens or user information.
Since many projects use automatic updates, some may have installed the compromised version without knowing. This makes the situation more serious. The attack also shows how one weak point can affect many systems at once.
What Developers Should Do Now?
Security experts urge developers to act quickly. First, check all dependencies and lockfiles. Look for the affected Axios versions and the malicious package. If found, remove them immediately. Then, switch to a safe version of Axios.
It is also important to review systems for unusual activity. Security teams must handle any signs of unauthorized access carefully. The npm registry has removed the harmful versions. But the incident is still under investigation. This attack is a clear reminder. Even trusted tools can become targets. In a fast moving space like crypto, staying alert is no longer optional.
Follow us on Google News
Get the latest crypto insights and updates.


